What is C2?
The term
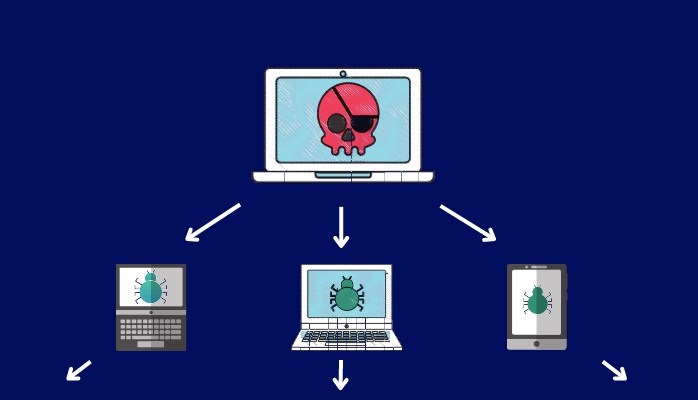
C2, or C&C, typically refers to Command and Control Infrastucture. It is the set of tools and techniques used by attackers to maintain control over a
compromised system following initial exploitation, and in order to exfiltrate sensitive data or perform other malicious activities.
Defending against C2-based attacks requires a multi-layered approach that involves a combination of technical controls, user awareness, and incident response processes. Here are some measures that can help defend against C2-based attacks:
Network Segmentation[a]: Segmentation of networks is a critical step in preventing the spread of malware and reducing the impact of a successful C2-based attack. This can be achieved by creating different security zones and limiting access between them.Endpoint Security[b]: Antivirus and anti-malware solutions can help prevent the installation and execution of C2-based malware on endpoints. Host-based firewalls can also help block C2 traffic.Intrusion Detection Systems[c]: IDS can help detect C2-based attacks by monitoring network traffic for signs of command-and-control communication.Incident Response Plan: Having a well-defined incident response plan that includes regular testing and updating can help mitigate the impact of a successful C2-based attack.Monitoring and Alerting: Proactive monitoring and alerting on suspicious network and system activity can help detect and respond to C2-based attacksPatches[d]: Keeping software and systems up-to-date with the latest patches and regular updates can help prevent attackers from exploiting known vulnerabilities to gain access to the system.User Awareness: Educating users on the risks associated with clicking on links or opening attachments in unsolicited emails or unknown sources can help prevent the initial infection of C2-based malware.By implementing these measures, organizations can significantly reduce the risk of falling victim to C2-based attacks and minimize the impact of any successful attacks.